
Intel is investigating the purported leak of much more than 20 gigabytes of its proprietary info and source code that a security researcher reported arrived from a details breach earlier this yr.
The data—which at the time this write-up went reside was publicly out there on BitTorrent feeds—contains facts that Intel makes offered to partners and consumers below NDA, a corporation spokeswoman mentioned. Talking on background, she mentioned Intel officers do not feel the knowledge came from a community breach. She also mentioned the enterprise is nonetheless making an attempt to identify how latest the content is and that, so considerably, there are no indications the details incorporates any shopper or individual info.
“We are investigating this situation,” organization officials mentioned in a statement. “The information appears to occur from the Intel Useful resource and Design and style Heart, which hosts info for use by our shoppers, companions and other exterior get-togethers who have registered for accessibility. We believe that an personal with accessibility downloaded and shared this information.”
Exconfidential Lake
The knowledge was posted by Tillie Kottmann, a Swiss application engineer who provided barebones aspects on Twitter. Kottmann has dubbed the leak “exconfidential Lake,” with Lake being a reference to the Intel insider name for its 10 nanometer chip platform. They explained they attained the facts from a supply who breached Intel previously this 12 months and that present day installment would be followed by other people in the potential.
“Most of the things right here have NOT been published Wherever in advance of and are classified as private, under NDA or Intel Restricted Secret,” Kottmann wrote. They stated some of the contents bundled:
- Intel ME Bringup guides + (flash) tooling + samples for numerous platforms
- Kabylake (Purley System) BIOS Reference Code and Sample Code + Initialization code (some of it as exported git repos with entire historical past)
- Intel CEFDK (Consumer Electronics Firmware Enhancement Kit (Bootloader things)) Resources
- Silicon / FSP resource code packages for various platforms
- Several Intel Progress and Debugging Equipment
- Simics Simulation for Rocket Lake S and possibly other platforms
- Various roadmaps and other paperwork
- Binaries for Digital camera motorists Intel designed for SpaceX
- Schematics, Docs, Applications + Firmware for the unreleased Tiger Lake system
- (incredibly horrible) Kabylake FDK education movies
- Intel Trace Hub + decoder documents for numerous Intel ME versions
- Elkhart Lake Silicon Reference and System Sample Code
- Some Verilog things for many Xeon Platforms, not sure what it is precisely
- Debug BIOS/TXE builds for various Platforms
- Bootguard SDK (encrypted zip)
- Intel Snowridge / Snowfish Approach Simulator ADK
- Several schematics
- Intel Marketing Substance Templates (InDesign)
- A lot of other factors
Material as current as May possibly
A fast overview of the leaked product reveals that it consists of private materials that Intel shoppers need to have to style motherboards, BIOS, or other issues that function with CPUs and other chips Intel helps make. Whilst we’re however analyzing the contents, we’re viewing style and design and test documents, supply code, and shows ranging from as early as Q4 2018 to just a couple of months in the past.
Most of these files and resource code packages use to Intel CPU platforms, like Kaby Lake or the future Tiger Lake, whilst there is a smattering of other files relating to other products and solutions, this kind of as a sensor offer Intel made for SpaceX.
There is also a folder dedicated to the Intel Management Engine, but its contents, way too, aren’t something Intel integrators don’t previously know. They’re check code and suggestions for when and how often to operate individuals automated exams whilst designing techniques that include an Intel CPU with the Intel ME.
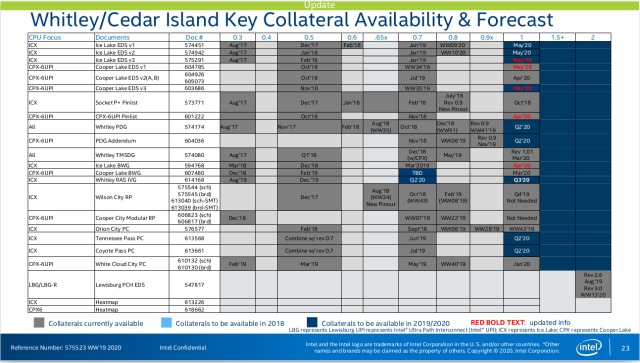
One of the dump’s newer bits included “Whitley/Cedar Island Platform Message of the 7 days,” dated May possibly 5. Cedar Island is the motherboard architecture that lies beneath both of those Cooper Lake and Ice Lake Xeon CPUs. Some of all those chips ended up unveiled earlier this 12 months, although some have nevertheless to turn into commonly available. Whitley is the dual-socket architecture for each Cooper Lake (14nm) and Ice Lake (10nm) Xeons. Cedar Island is for Cooper Lake only
The contents include things like a good deal of diagrams and graphics like the just one underneath:
Some contents provide a cryptic reference to voltage failures in some Ice Lake samples. It’s not crystal clear if the failures implement to true components sent to shoppers or if they are happening on reference boards Intel provided to OEMs for use in developing their very own boards.
How done it?
Though Intel claimed it doesn’t believe that the documents ended up received by way of a community breach, a screenshot of the dialogue Kottmann had with the supply supplied an alternate explanation. The resource claimed that the paperwork were being hosted on an unsecured server hosted on Akamai’s content material delivery network. The source claimed to have recognized the server applying the nmap port-scanning resource and from there, made use of a python script to guess default passwords.
Here’s the discussion:
resource: They have a server hosted on the net by Akami CDN that was not adequately secure. Right after an internet huge nmap scan I observed my concentrate on port open up and went by means of a listing of 370 possible servers centered on information that nmap offered with an NSE script.
resource: I employed a python script I built to probe different factors of the server including username defaults and unsecure file/folder accessibility.
resource: The folders were just lying open up if you could guess the title of a single. Then when you had been in the folder you could go again to root and just click on into the other folders that you failed to know the identify of.
deletescape: holy shit that’s exceptionally amusing
supply: Ideal of all, because of to one more misconfiguration, I could masqurade as any of their staff or make my individual person.
deletescape: LOL
resource: Yet another amusing matter is that on the zip data files you may possibly locate password guarded. Most of them use the password Intel123 or a lowercase intel123
resource: Security at it’s greatest.
Kottmann said they did not know the resource effectively, but, dependent on the evident authenticity of the materials, you will find no purpose to doubt the source’s account of how it was received.
The Intel spokeswoman didn’t quickly provide a response to the assert.
Many onlookers have expressed alarm that the resource code has opinions that contains the phrase “backdoor.” Kottmann instructed Ars that the phrase appeared two moments in the supply code associated with Intel’s Purely Refresh chipset for Xeon CPUs. So significantly, there are no acknowledged analyses of the resource code that have identified any covert solutions for bypassing authentication, encryption, or other protection protections. Aside from, the term backdoor in coding can sometimes refer to debugging features or have other benign meanings.
Individuals are also lampooning the use of the passwords Intel123 and intel123. These are no doubt weak passwords, but it is not likely their function was to safe the contents of the archive data files from unauthorized persons.




More Stories
Why Information Technology is Key to Growth
Information Technology: Your Pathway to Innovation
Unlocking the Future of Information Technology