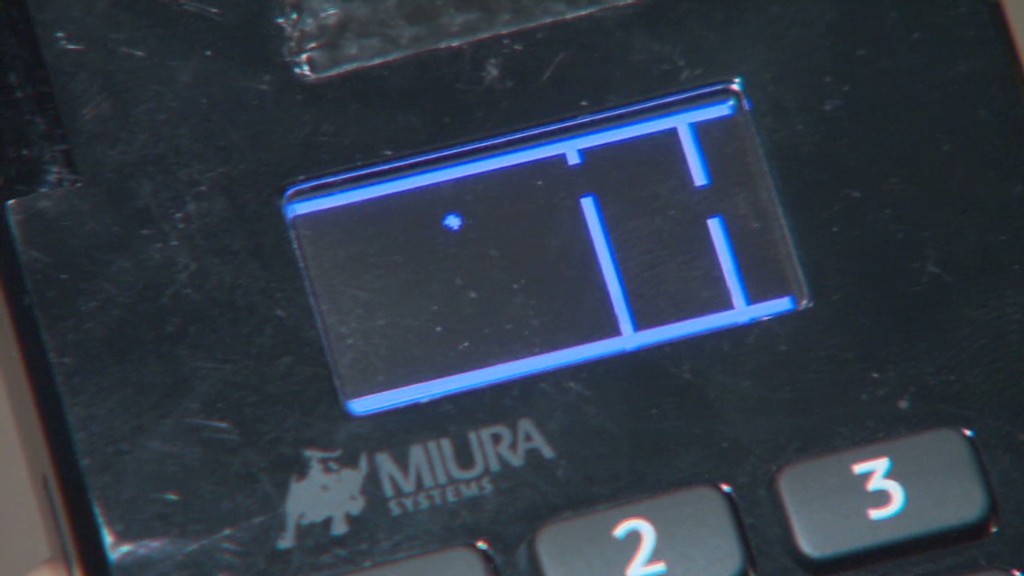
Get all set for a facepalm: 90% of credit rating card audience at present use the exact password.
The passcode, established by default on credit score card equipment since 1990, is very easily located with a rapid Google searach and has been uncovered for so extensive there is no feeling in hoping to cover it. It truly is either 166816 or Z66816, based on the device.
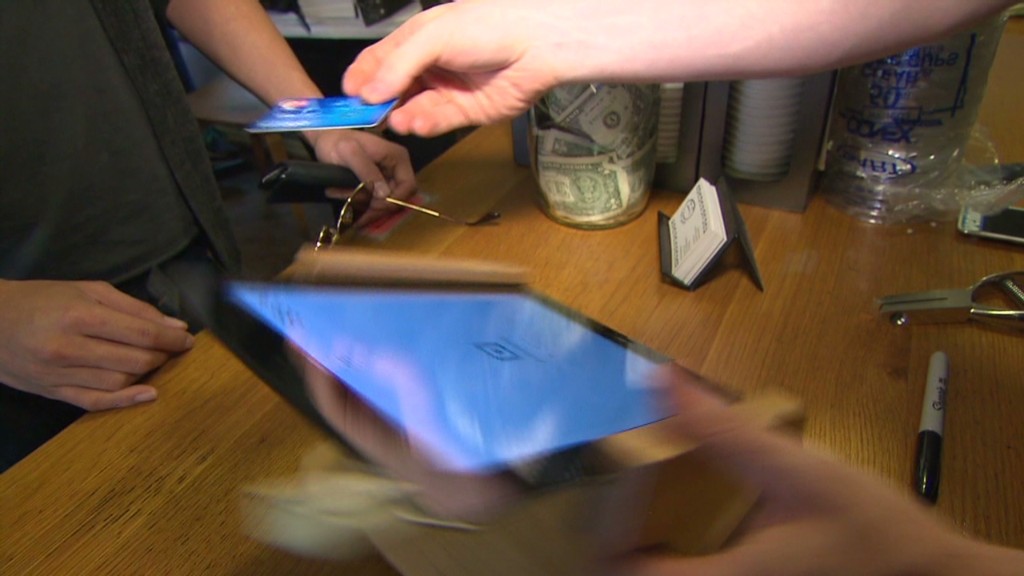
With that, an attacker can attain comprehensive management of a store’s credit card viewers, perhaps permitting them to hack into the devices and steal customers’ payment details (consider the Concentrate on (TGT) and Residence Depot (Hd) hacks all in excess of once again). No surprise major stores keep dropping your credit score card information to hackers. Protection is a joke.
This newest discovery will come from scientists at Trustwave, a cybersecurity company.
Administrative entry can be applied to infect devices with malware that steals credit rating card facts, described Trustwave govt Charles Henderson. He detailed his conclusions at previous week’s RSA cybersecurity convention in San Francisco at a presentation named “That Position of Sale is a PoS.”
Acquire this CNN quiz — locate out what hackers know about you
The problem stems from a activity of scorching potato. Product makers sell machines to special distributors. These vendors market them to shops. But no a single thinks it truly is their job to update the master code, Henderson told CNNMoney.
“No 1 is switching the password when they established this up for the initial time everybody thinks the protection of their point-of-sale is somebody else’s duty,” Henderson claimed. “We are creating it quite easy for criminals.”
Trustwave examined the credit history card terminals at extra than 120 suppliers nationwide. That incorporates significant apparel and electronics shops, as perfectly as area retail chains. No distinct suppliers were being named.
The vast greater part of machines have been designed by Verifone (Pay out). But the exact situation is current for all significant terminal makers, Trustwave reported.

A spokesman for Verifone reported that a password by yourself just isn’t sufficient to infect equipment with malware. The business claimed, until finally now, it “has not witnessed any assaults on the protection of its terminals based mostly on default passwords.”
Just in situation, while, Verifone reported retailers are “strongly recommended to transform the default password.” And today, new Verifone devices come with a password that expires.
In any case, the fault lies with merchants and their distinctive suppliers. It can be like dwelling Wi-Fi. If you obtain a house Wi-Fi router, it can be up to you to transform the default passcode. Stores ought to be securing their personal machines. And device resellers should be assisting them do it.
Trustwave, which will help protect retailers from hackers, explained that keeping credit score card machines safe and sound is small on a store’s record of priorities.
“Corporations commit extra cash choosing the coloration of the stage-of-sale than securing it,” Henderson reported.
This trouble reinforces the summary designed in a latest Verizon cybersecurity report: that merchants get hacked for the reason that they are lazy.
The default password point is a severe challenge. Retail personal computer networks get uncovered to laptop viruses all the time. Contemplate a single circumstance Henderson investigated lately. A horrible keystroke-logging spy software package ended up on the laptop or computer a retail store uses to process credit rating card transactions. It turns out personnel had rigged it to play a pirated version of Guitar Hero, and unintentionally downloaded the malware.
“It displays you the amount of access that a great deal of people have to the position-of-sale surroundings,” he stated. “Frankly, it’s not as locked down as it need to be.”
CNNMoney (San Francisco) To start with revealed April 29, 2015: 9:07 AM ET




More Stories
Growing Small Businesses with Virtual Assistant Services
Strength and Versatility of Chain Link Fences in Ocala, FL
Why Hiring a LinkedIn Marketing Agency Can Accelerate Your Business Growth